Examining the Shadowy Corners of Cybersecurity: Unraveling the Enigma of Security Vulnerabilities
Well, howdy—hold your horses now! If you're scouting about for the inside scoop on cybersecurity and specifically, the labyrinthine world of security vulnerabilities, you're in the right place. Together, we will embark on a whirlwind tour – a cliff-hanging roller-coaster, if you will—around this puzzling topic, as featured in the CompTIA Security+ (SY0-601) exam. Tighten your seat belts, it's gonna be one heck of a ride!
Mapping the Terrain of Security Vulnerabilities
Ah, security vulnerabilities! These are the tricky little holes, the secretive trapdoors through which our cyber adversaries sneak into our systems, leaving a mess behind. They are like the moth-eaten holes in your favorite woolen sweater, letting in the freezing winter chill. Let's put our Sherlock Holmes hat on and detect these infernal loopholes—knowing is half the battle, after all.
The Big Bad Wolves: Types of Vulnerabilities
Jumping headfirst into the deep end, we'll tackle the many types of vulnerabilities and their associated security concerns.
First off, we have software vulnerabilities. You know, bugs that crawl into the code and wreak havoc like a bull in a china shop. These bugs can jump out at you from the most innocuous-looking piece of software—yes, even your beloved photo-editing app!
Then, we can't forget about hardware vulnerabilities. It's not just your softwares that can betray you; your physical equipment might just join in the treachery too! Be it an aging router, an innocuous printer, or a subtly compromised USB—Hardware vulnerabilities are like silent, invisible spies living amongst us, waiting for the perfect moment to strike.
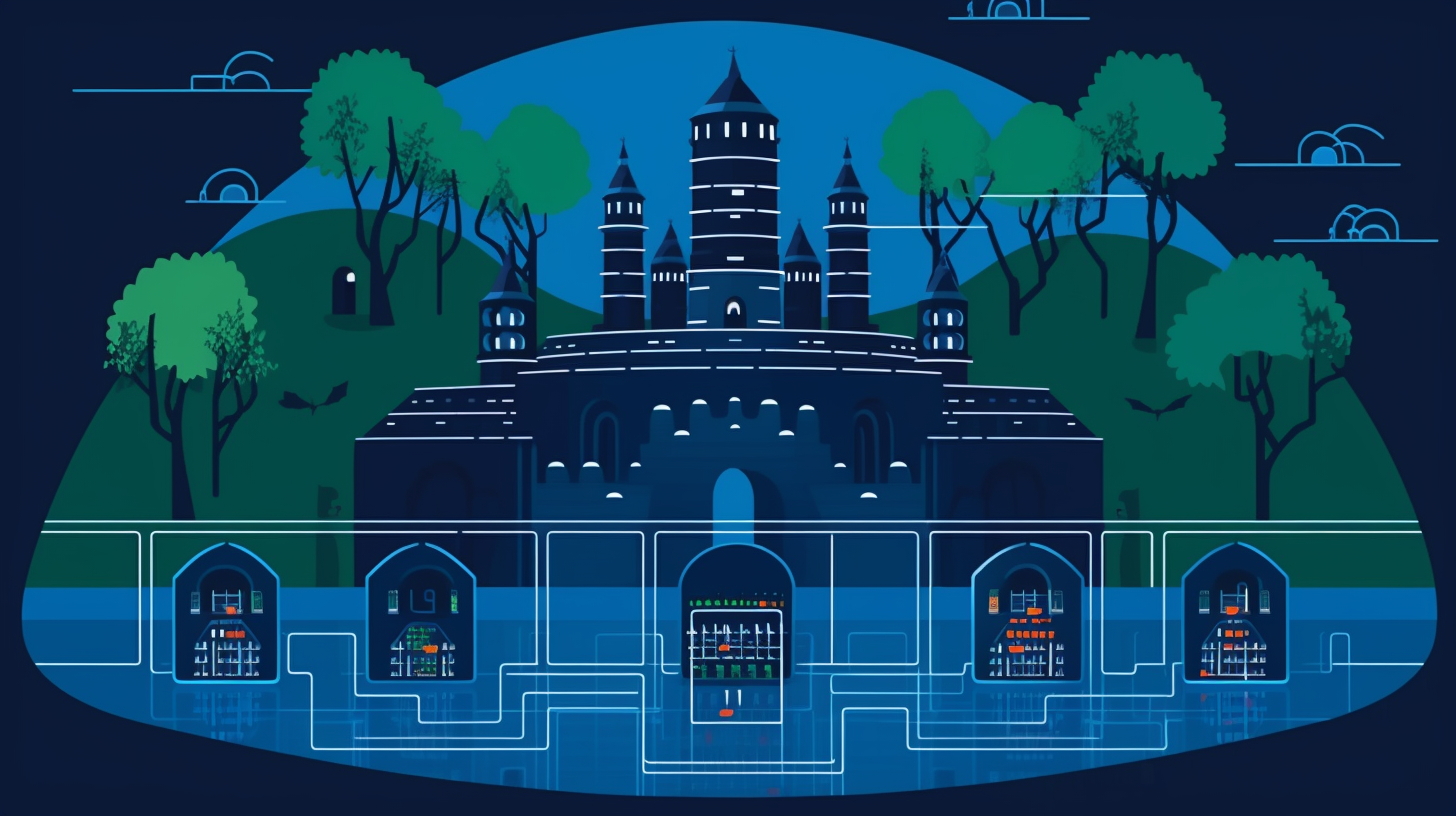
Last but not least, we have network vulnerabilities. Imagine your network as a castle—we have the faithful guards (firewalls), the sturdy walls (encryption), and the moat filled with alligators (intrusion detection systems). But guess what? A castle is not impregnable. The enemies can still sneak in through a secret passage or disguise themselves as friends. That's what network vulnerabilities do—they bypass your defenses, leaving you exposed.
Peekaboo! Security Concerns Associated with Vulnerabilities
What's the big fuss about these vulnerabilities anyway? Well, there's a whole kettle of fish waiting to be fried when it comes to security concerns.
For starters, vulnerabilities could lead to data breaches. Imagine your confidential data—trade secrets or customer information—being aired out like dirty laundry. Doesn't paint a pretty picture, does it?
Then there's the issue of system downtime. When attackers target your systems, they could potentially shut them down, leaving you in a pickle. And let's not forget, every tick of the clock equates to cash.
Plus, let's not forget about damage to credibility and trust. In the unpredictable frontier of the internet, trust stands as the highest form of currency. If you squander your customers' trust, you can't recapture it. So, the price tag on a security vulnerability could surpass your wildest estimations.
To the Rescue - Mitigation Strategies
Shall we permit these cyber attackers to proceed unchecked? No siree! We need to put up a good fight and mitigate these security vulnerabilities.
About software vulnerabilities, prevention is better than cure. Regular patching and updating (we're looking at you, Adobe) is a must. Throw in some good security practices like not downloading from sketchy sources, and we're halfway there.
As for hardware vulnerabilities, keeping our devices up-to-date and properly configured can nip most problems in the bud. Don't forget, decades-old routers are no good in today's cyber landscape!
Last but not least, for network vulnerabilities - who are we kidding, we need an army! Firewalls for inspection, intrusion detection systems for alerting, robust encryption to keep conversations private — the whole shebang!
That sums it up, folks. There you have it—that's the essentials on security vulnerabilities. Keep in mind, preparing for cybersecurity isn't a frill—it's a crucial need in our tech-saturated era. As you lace up your boots to face the CompTIA Security+ (SY0-601) exam, keep your chin up and aim to hit it out of the ballpark!