Decoding the Enigma: A Comprehensive Guide to Security Architectures
Have you ever gazed upon a security architecture, only to declare it a baffling jumble of technical jargon? Well, rest assured, many walk in those same puzzled shoes! Together, we'll plunge headfirst into this labyrinth, and believe you me: when we emerge, a fully-fledged security architect will stand in your shoes, armed to slay the dragon known as the CCNA 200-301 exam. With a pinch of wit, a dash of charm, and an undying love for metaphors, let's embark on this epic journey together.
The Magnificent World of Security Architectures
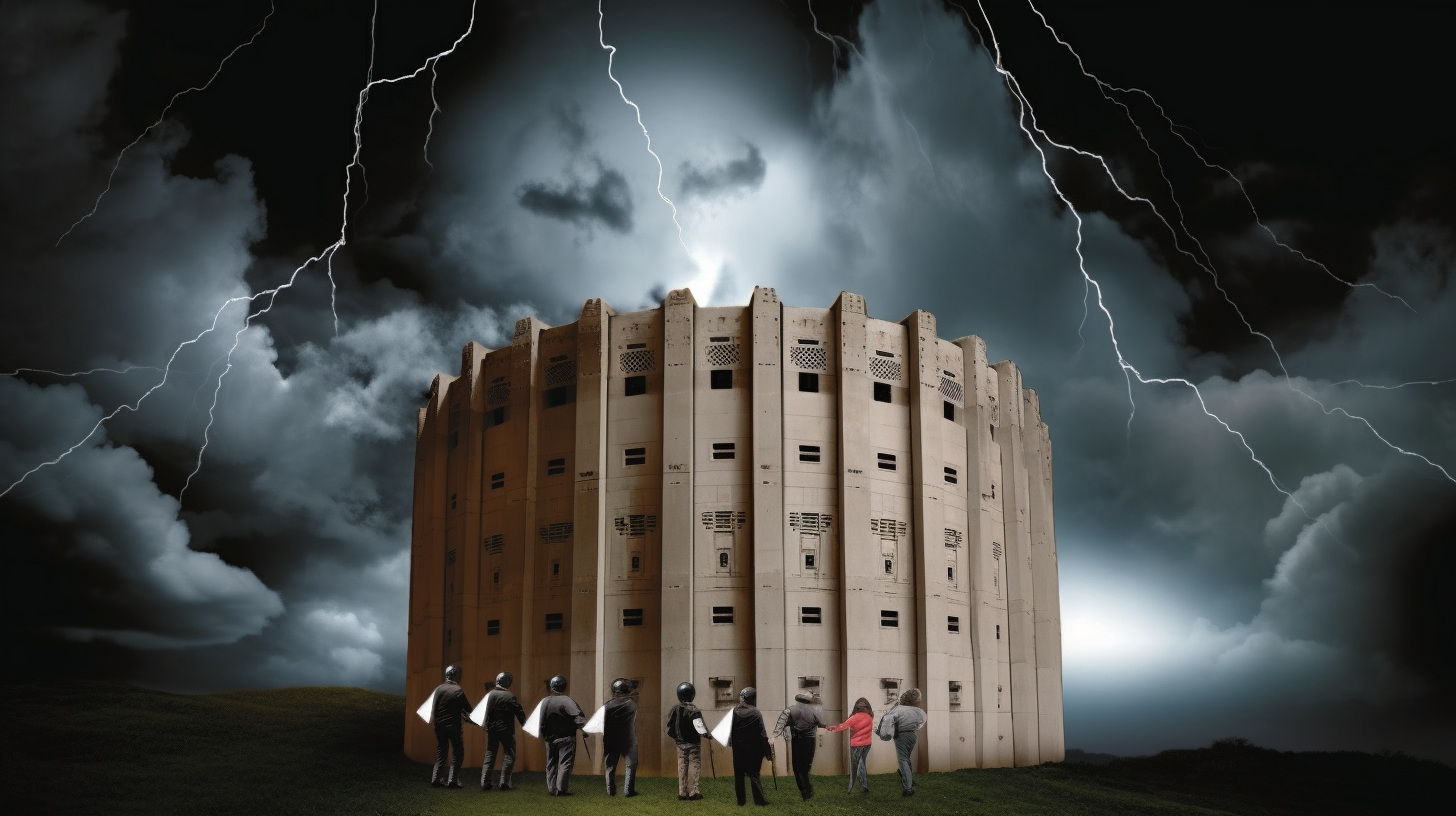
Picture this: Security architecture is like a mighty fortress, watching over your precious kingdom (network, system, what have you) with eagle eyes. Its thick stone walls (firewalls, in our case) stand tall and unyielding - a formidable deterrent for any would-be invaders. And it's not just the walls. The fortress is armed to the teeth with an array of sophisticated traps (intrusion prevention systems) and watchful sentries (systems, protocols, and processes that maintain network security).
But hey, what's a fortress without a robust blueprint? That's where a good security architect enters the fray; designing those fortresses and ensuring they can weather any storm. Remember, security architectures aren't merely massive barriers and alert sentries; they form the bedrock of a steadfast network. And to truly understand such a foundation, one must commence from the ground up.
The Underbelly: Secure Network Foundation
Think of a secure network foundation as the foot soldiers of our fortress. They're the frontline defence against external threats and internal blunders alike. These brave soldiers encompass everything from antivirus software and firewalls to multilevel security strategies and incident response teams. However, they don't work alone. It's vital to have a thorough understanding of every asset in your network - akin to knowing every soldier’s strengths and weaknesses - to create a robust, coordinated defence.
Take VLANs, for instance, those valuable handmaidens of network segmentation. They help compartmentalize your infrastructure, ensuring that even if a sneaky invader breaches one segment, the rest of your network remains unconquerable. Another critical piece of this puzzle is a powerful incident response strategy. It's akin to having a knight in shining armor, riding to your rescue if, heaven forbid, all your defences fail. Remember folks, in the kingdom of network security, there's no such thing as too prepared.
The Heart: Security Principles and Policies
What governs the soldiers? What directs the knight in the midst of a chaotic battle? That's right, it's a kingdom's principles and policies - the very heart of any security fortress. They provide guidelines that outline how to defend the realm, ensuring every asset responds to threats with the right blend of might and diplomacy. Understanding these principles is absolutely vital for any security architect. Without it, you're like a rudderless ship, tossed about in the stormy sea of potential security threats.
Consider the principle of least privilege, for example. It's like a wise old king who only entrusts enough power to his subjects necessary for their assigned duties, and no more. Why tempt fate and risk power falling into the wrong hands, right? Then, there are policies like password and user access control. They're like the gatekeepers of the castle, carefully scrutinizing everyone who wants to enter. Dilly dallying with these policies is not an option unless you fancy a visit by unexpected gate crashers!
The Funny Side of Security Architectures
Now, let's inject a little humor into these austere annals of security. Imagine – a day in the life of a security architect as narrated by an overexcited superhero fan. Our modest security architect wakes up to an ear-piercing alarm at the crack of dawn. With a steaming cup of java in hand, he stares at his computer screen, transforming before our very eyes into... SecurityMan!
Armed with his superhero cape (a comfy bathrobe), he patrols the dark recesses of the internet, battling the dastardly DDoS attacks and dispelling the wicked Malware minions. No firewall is too high, no encryption too complex for our valiant hero. And the folks at work? They're none the wiser, unaware of the epic battles fought and won before their first cup of coffee!
Preparing for the Battle: CCNA 200-301
Aspiring SecurityMen and SecurityWomen, the CCNA 200-301 exam is your final frontier before you don the cape. Decoding multi-layered security solutions, understanding arcane protocols, networking security gadgets – it’s no cakewalk, and who said it would be? It's your rite of passage, your personal Ordeal by Fire (or in this case, by Cisco) that you need to endure to emerge as a true champion of security.
Take heart! Embrace the challenge, arm yourself with knowledge, and keep your sense of humor. Remember, learning can be a joyride, and even the trickiest security conundrums are no match for a determined mind and a light heart. So go on, take the leap, and unravel the mysteries of security architectures. Master the art, become the architect, and remember - the world (or at least your network) is your fortress!